开篇
故事背景是这样,出租屋那里有一只RB750G r3做出口路由器,之前由于互联网线路是300M的,所以在配置方面,是比较随意,就真把这小东西当成一个能5个口都跑满线速度的路由器来规划接口的链接方式了。
可是,最近由于电信将宽带免费(是的,只要满足月消费多少多少,就免费)提升到1000M下行还有50M的上行,这时候,之前那随心所以的配置方法,就会让这只路由器的转发能力下降。于是我废了相当大的功夫(这文档写的十分隐晦,非常难读懂),进行了一番优化,终于还是能发挥出其全部性能,跑到900M也不是什么大问题。(包含一定的防火墙策略,不是简单的裸奔)
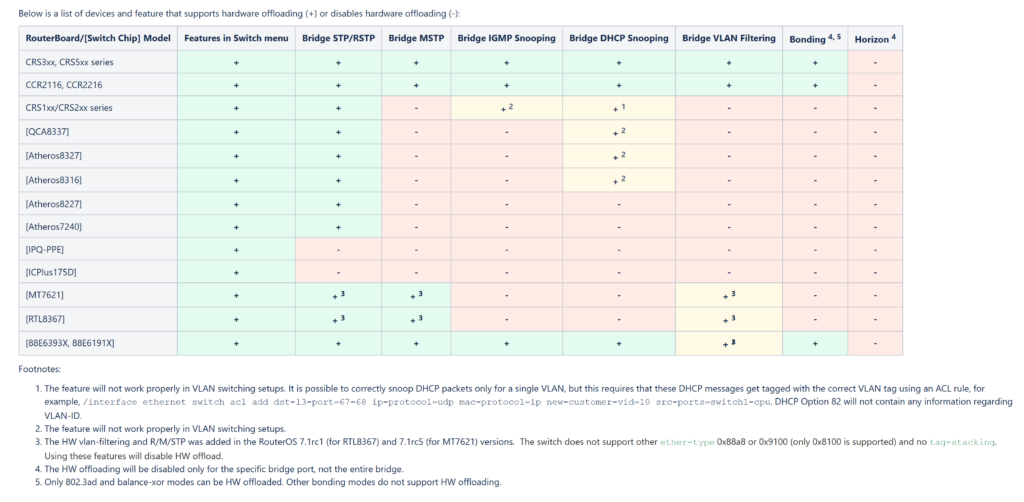
首先,还是上相关资料:
这个路由器非常的奇怪,Mikrotik提供了2个block-diagram,具体怎么翻译这个不好说,但从结果来看的话,我觉得可以翻译成“硬件拓扑图”
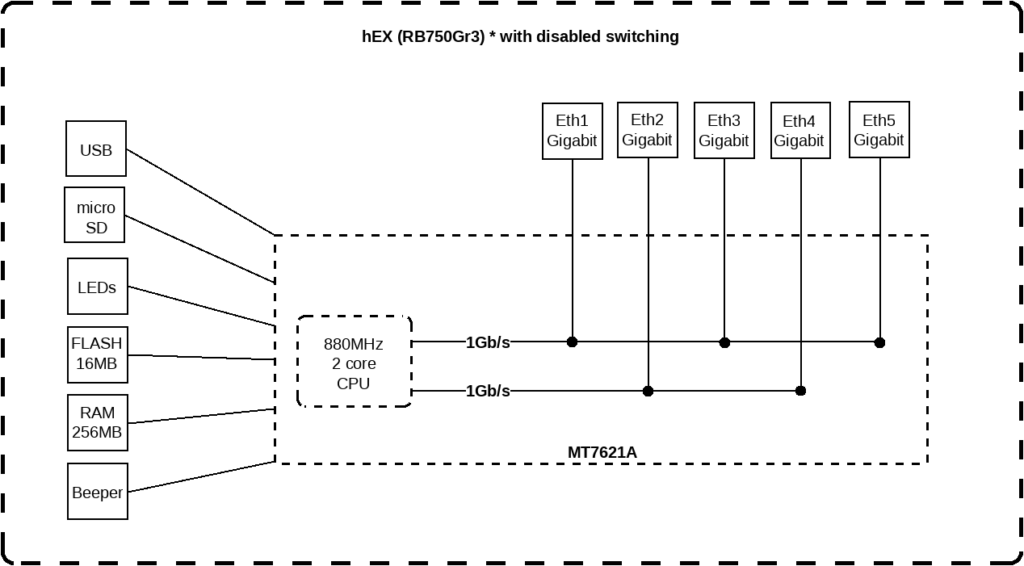
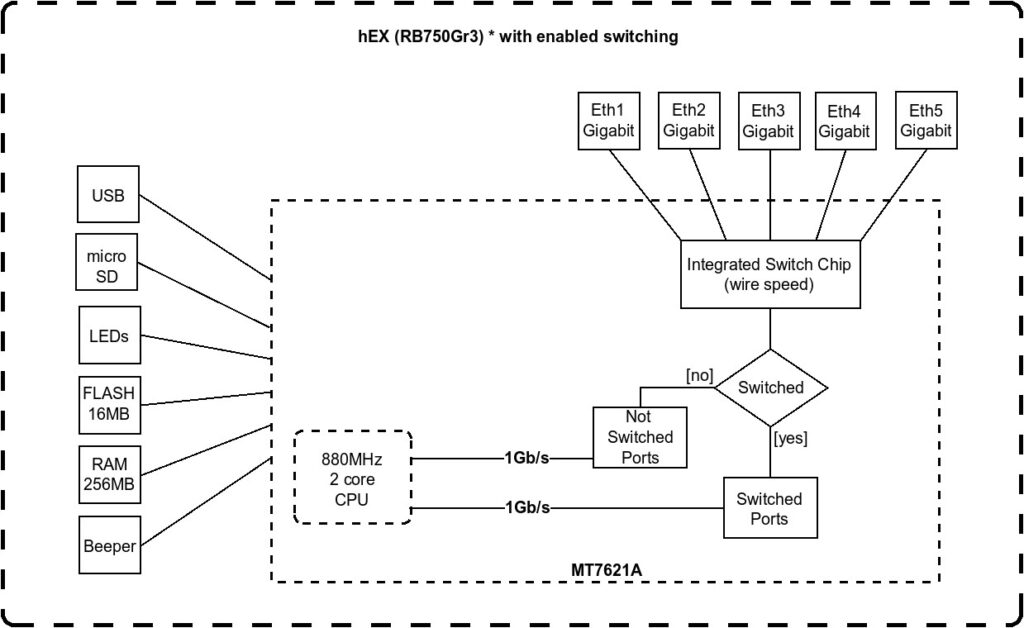
根据分布图,明显是启用“交换”的时候,能够发挥最大的性能,1个上行口,其余4个交换,那么对于CPU来说就是1Gb/s入,1Gb/s出,非常合理。
但是要怎么打开这个“交换”呢?产品页面里面没有任何说明……
于是经过一番苦苦搜索,我找到了第二个链接,里面介绍了一位前辈的操作过程,里面提到了一个很重要步骤:
Make sure the bridge is created without spanning tree enabled (ie, no STP/RSTP/MSTP) as the switch chip cannot handle that, and so using those features will force slow software switching. The default mode is RSTP, which will turn off hardware switching on several chipsets, including the RB750Gr3/hEX one.
你的bridge需要关掉STP。哈啊?这玩意不是默认打开的吗?于是我自己看来一下:
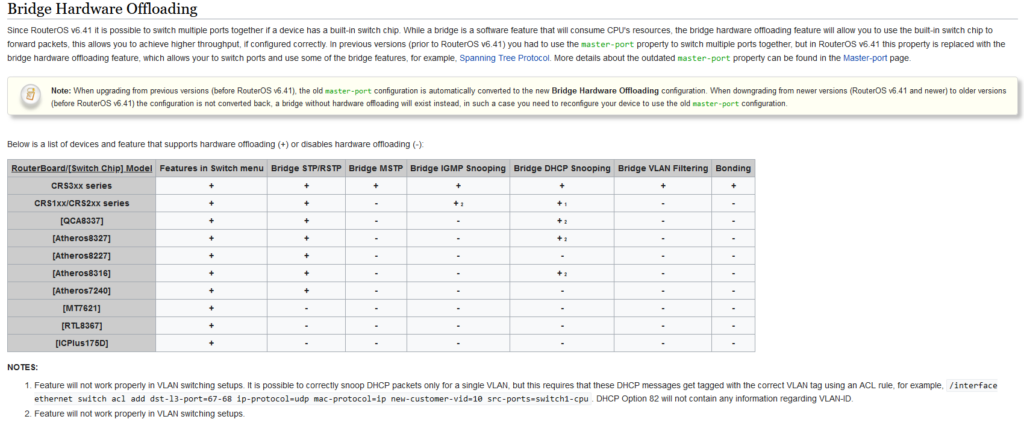
我丢,这玩意用的MT7621,由于不支持这些那些功能,所以呢,必须要关掉,否则的话,就会变成内核转发。我想我大概找到问题所在了。
规划
首先,重新规划好端口,按照1上行,4下行的方式划分端口,下行的4个接口都划分到同一个bridge,多子网的情况下,可以用vlan接口或者是做静态路由。
规划过程中有这几点需要注意(仅对于Ros v6有效,Ros v7有改进,可能有更多功能,但是由于是生产环境我暂时还不敢升级):
- 建议只使用一个bridge,因为只有1个bridge能off-load到硬件
- 不支持给没vlan标签的包加上vlan标签,即所有access口都只能在同一个vlan,和bridge(无vlan标签)处于同一个子网
- 不能使用链路聚合
- 不能使用QinQ
打开“交换”
调整交换机的配置,检查一下多余的功能是否都已经关闭,必要的功能都打开:
- bridge的protocol-mode必须是none
- bridge的igmp-snooping必须是no
- bridge的dhcp-snooping必须是no
- bridge的vlan-filtering必须是no
- /interface bridge settings里面allow-fast-path必须是yes
- /ip settings里面allow-fast-path必须是yes
配置示例
下面是一个示例的命令行:
/interface bridge
add name=local protocol-mode=none vlan-filtering=no
/interface bridge port
add bridge=local interface=ether2
add bridge=local interface=ether3
add bridge=local interface=ether4
add bridge=local interface=ether5
/interface bridge vlan
add bridge=local untagged=local,ether2,ether3,ether4 vlan-ids=1
add bridge=local tagged=local,ether4,ether5 vlan-ids=2
add bridge=local tagged=local,ether4,ether5 vlan-ids=3
/interface vlan
add interface=local name=guest vlan-id=2
add interface=local name=server vlan-id=3
/ip address
add address=192.168.1.1/24 interface=local
add address=192.168.2.1/24 interface=guest
add address=192.168.3.1/24 interface=server
以上是一个简单的示例,创建了一个bridge,2口和3口都是Access模式,划分到一个子网里面。4口是hybrid模式,没有vlan标签的包,会和2、3口处于同一个子网,同时,能够接受带vlan-id=2的包。5口也是Trunk模式,分别接受vlan2和vlan3的包。然后创建了2个vlan接口,“guest”、“server”。然后local、guest、server3个接口都配置了ip地址。
顺利的话,就能在/interface bridge port print里面看到行的开头有个H的标识,代表已经使用了硬件卸载。同时,系统日志里面也会有相关提示。
测速结果
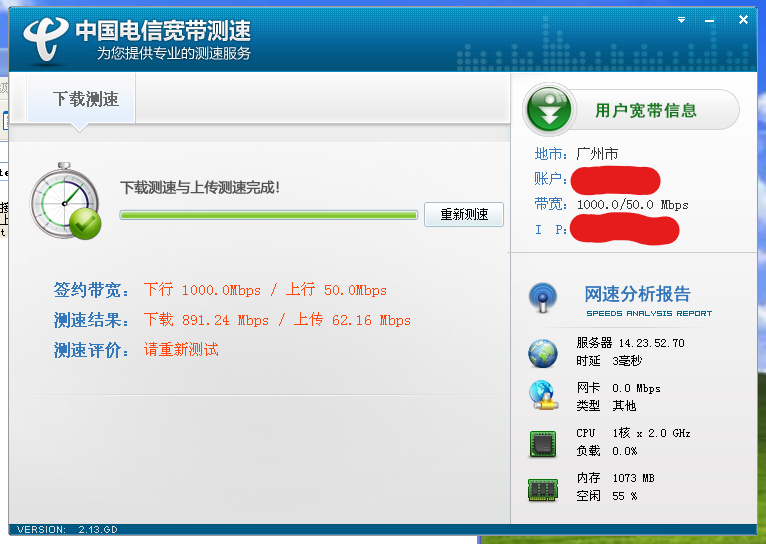
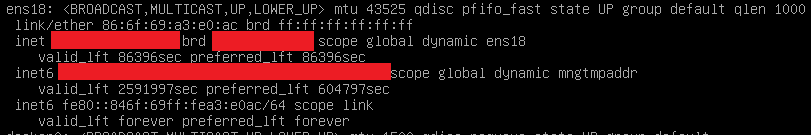
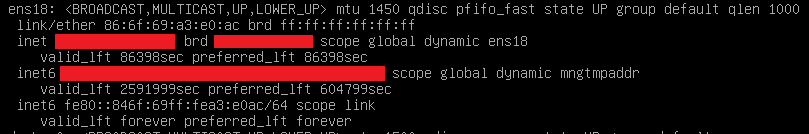
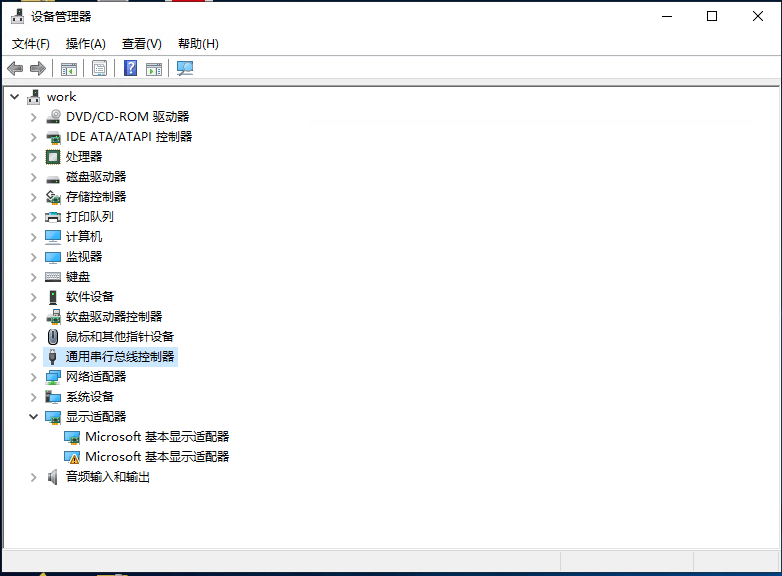
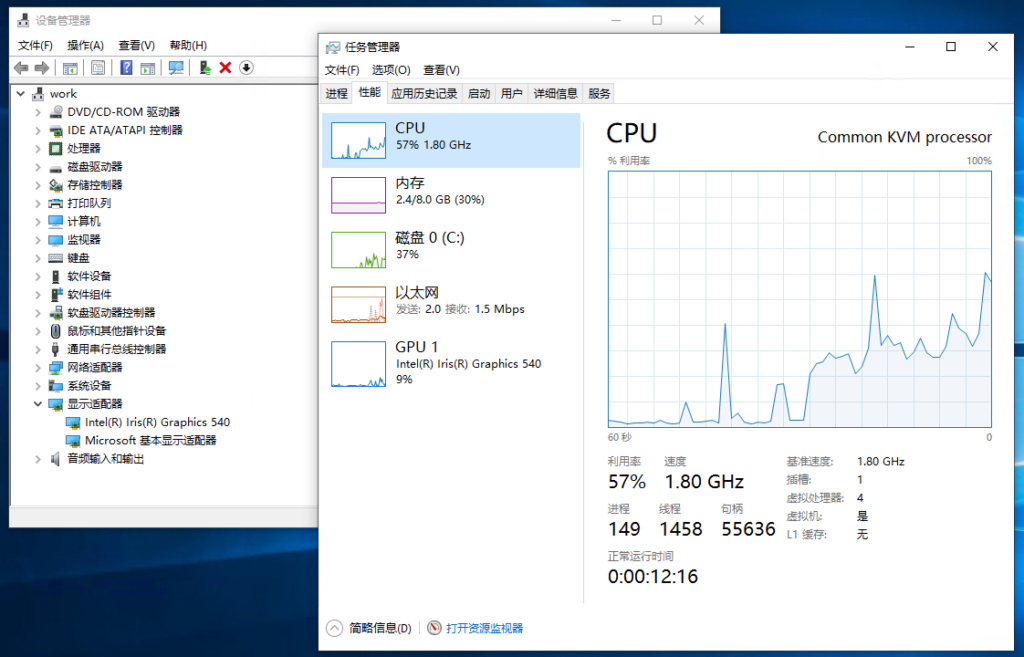
J4125的小主机上分了1核心+1G内存的XP,跑了以上的测速结果,期间基本上没其他人同时用网。也基本上差不多了吧。
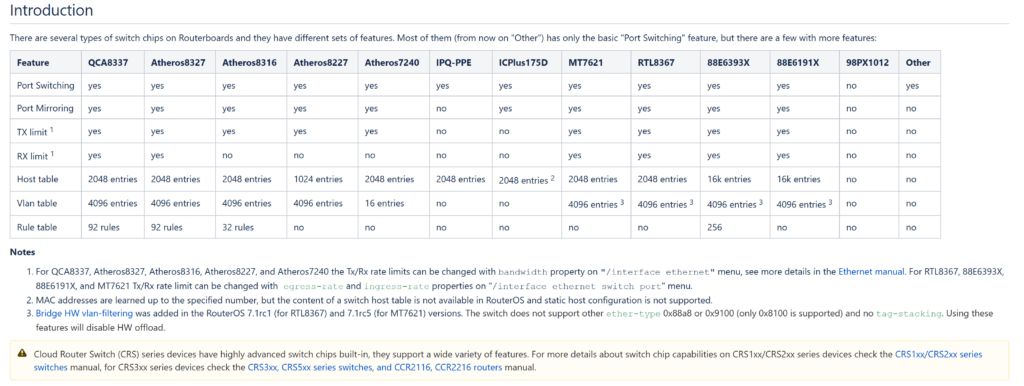
Ros V7更新
自从RouterOS v7.1rc5之后,MT7621(就是RB750Gr3所使用的CPU/交换芯片),更新了驱动,支持了vlan表,所以,可以给access口的包打标签了。另外的话,也提供了STP的硬件支持。
对比v6的设置,有这么一些不同:
- bridge的protocol-mode可以是STP/RSTP/MSTP
- bridge的igmp-snooping必须是no
- bridge的dhcp-snooping必须是no
- bridge的vlan-filtering可以是yes
- /interface bridge settings里面allow-fast-path必须是yes
- /ip settings里面allow-fast-path必须是yes
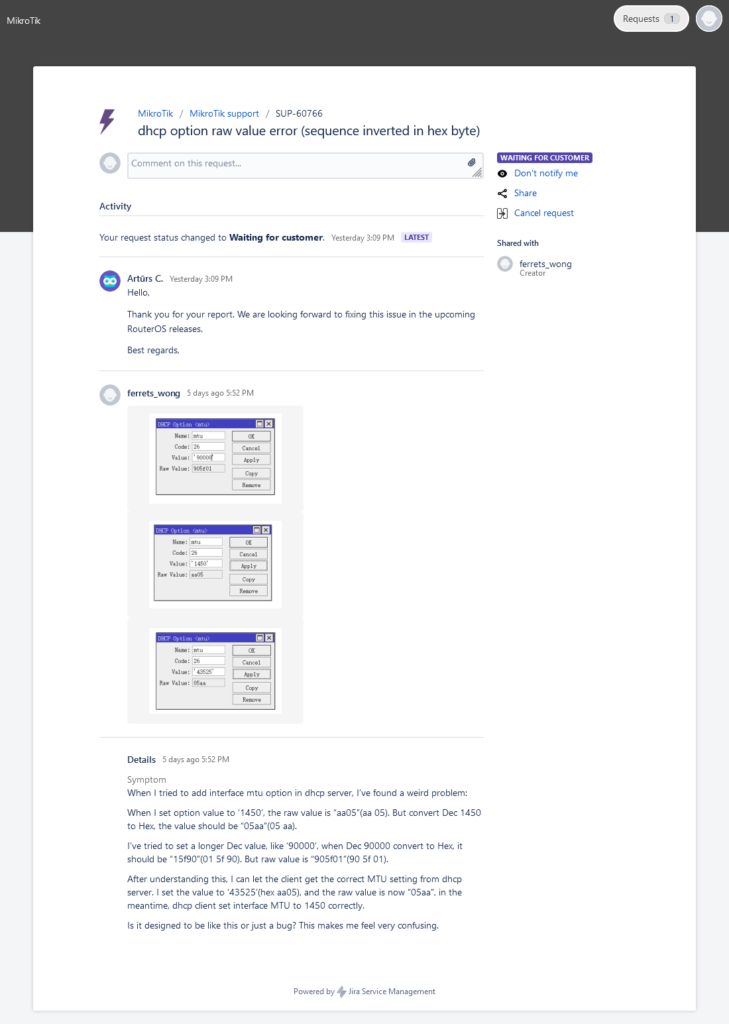
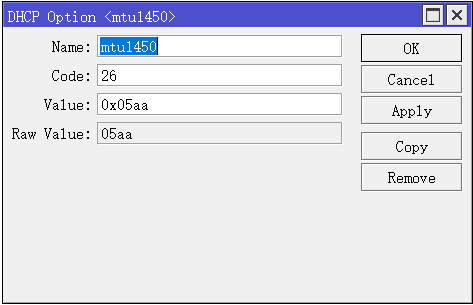
重点注意
根据观察和mikrotik的论坛报告,系统更新到了Ros V7之后,转发性能有所下降,根据我观察所得,基本上从之前的约800+Mbit/s下降到了600~700Mbit/s,感觉有点难受。
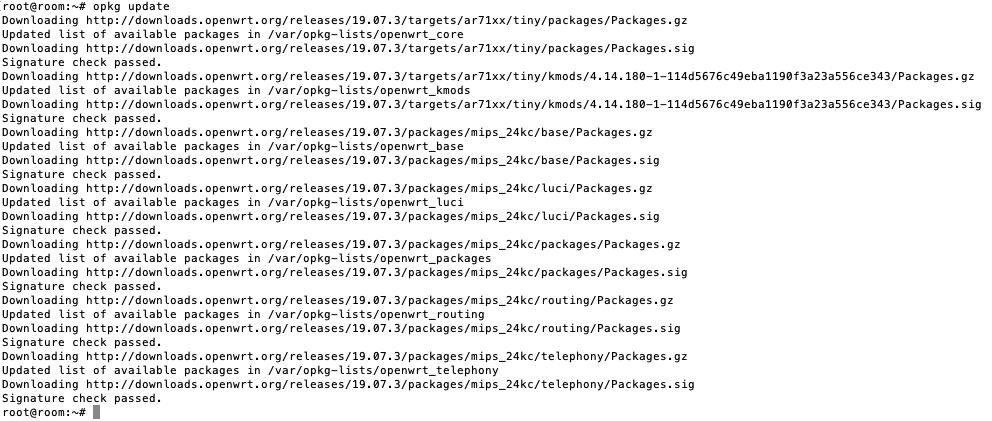
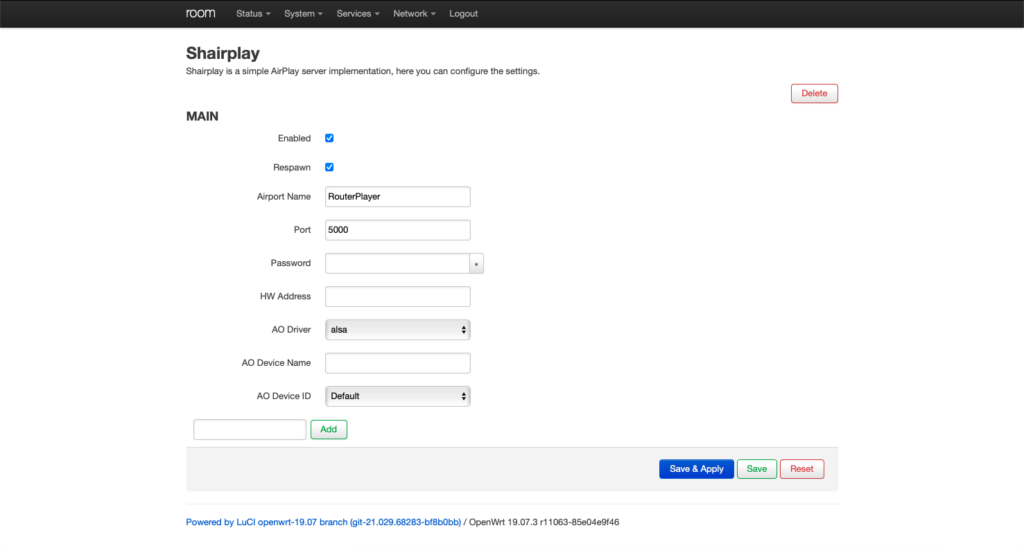
不过偶然间,我发现了一个油管视频:https://www.youtube.com/watch?v=bllvDWEKgNA,还有论坛里面的一些帖子:https://forum.mikrotik.com/viewtopic.php?p=959710#p959710,里面提到,这机器刷了OpenWRT之后,可以打开硬件转发,可以在跑满950+Mbit/s转发的情况下,99% CPU idle。就是说,如果Mikrotik继续开发,是可以将l3hw下放到这个小机器上的。不过……鬼知道要等到什么时候。
配置示例.v7
/interface bridge add name=local protocol-mode=RSTP vlan-filtering=yes /interface bridge port add bridge=local interface=ether2 add bridge=local interface=ether3 add bridge=local interface=ether4 add bridge=local interface=ether5 /interface bridge vlan add bridge=local tagged=local,ether5 untagged=ether2 vlan-ids=1 add bridge=local tagged=local,ether5 untagged=ether3 vlan-ids=2 add bridge=local tagged=local,ether5 untagged=ether4 vlan-ids=3 /interface vlan add interface=local name=lan vlan-id=1 add interface=local name=guest vlan-id=2 add interface=local name=server vlan-id=3 /ip address add address=192.168.1.1/24 interface=lan add address=192.168.2.1/24 interface=guest add address=192.168.3.1/24 interface=server
例子中,ether2、ether3、ether4均为access口,ether5为trunk口。划分了3个vlan,分别名字为lan、guest、server。